In times like these, we are always open to different types of cyber security threats. The nature of these threats is rapidly changing as we sink deeper into the digital global village.
They exist in the shells of our virtual worlds, poised to pounce on us at a moment when we least suspect.
The purpose of this blog is to reveal these different types of cyber security threats surrounding this disease, enabling you to recognize the signs and to take action that can sufficiently defend against this disease.
We’ll run through the different types of cyber attacks starting from the most well-known to the more complicated ones and give you a complete understanding of why they occur and what their pattern is.
Learning those risks enables carrying out preventive actions necessary for secure online performance.
Table of Contents
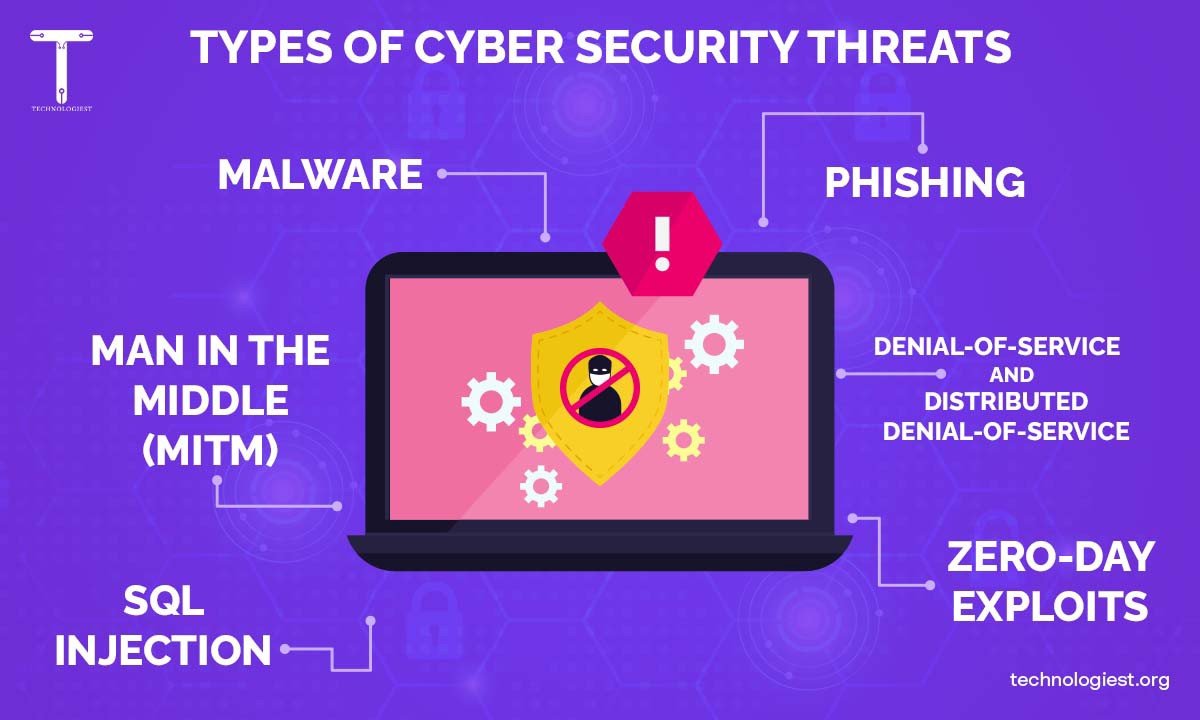
ToggleMost Dangerous Types of Cyber Security Threats

Cybersecurity threats put their stamp on cyberspace and these threats have a very marked language.
Though it may not be readily apparent, There are many types of cyber security threats.
These threats can be manifested in different shapes ranging from viruses primarily used to corrupt our files, phishing schemes employed to steal our personal information, to ransomware that can encrypt our data and refuse to return it unless we pay the ransom.
They are the digital whirlwind that can and does end in havoc within our peaceful online community.
Sometimes you may feel unprepared for these quick and unexpected changes but think of them as providing you with experience.
We will hunt for these digital wolves in today’s digital forest with confidence.
Malware
Malware is one of the most common types of cyber security threats so it is logical to assume that every once in a while, all of us face this threat during our digital trips.
As a modern digital equivalent to the common cold, malware (short for malicious software) can keep any user up all night searching for solutions.
It refers to the umbrella term that encompasses any software that is created maliciously to infect and devastate machines, servers, clients, or computer networks.
From messing up your system to stealing your valuable files, malware has the potential to deal with lots of problems.
Malware includes viruses that can infect and alter your files, worms that can spread across a network, and Trojans that can backdoor your security.
However, this raises the question of how this cyber villain gets its route.
It commonly hides through fraud links, and infected software downloads on attachments, that appear to be legitimate.
It functions like that of a remote control, exploiting you into unconsciously installing it on your device.
Being informed about malware variants and types is a good beginning of the road to safe cyber activities.
Phishing
Let’s now broaden our minds to Phishing, another type of cyber security threat that threatens cyber security.
Phishing is a poisoned bait that criminals use in order to get you to disclose your personal or sensitive data.
It’s a technological trick: the bait is an e-mail or a message, while it is believed the receiver trusts the source.
The puppeteers of cyber criminals riding on a phishing scheme are digital puppet masters.
They get hold of you and manage your mind, pushing you into forwarding all your personal information.
Such data is by names, passwords, credit number cards, and other information that can be exploded, illegally even.
Phishing is one unethical way in which scammers ask you to click on a malicious link and give your personal details by pretending that your bank account has been compromised.
Having a knowledge of phishing and the process is very important, as it will safeguard you from getting your identity stolen.
Man in The Middle (MitM)
And here comes the time to get through the charged waters of Man-in-the-Middle (MITM) Attacks, another major type of cyber security threats.
A Man-in-the-Middle assault is an example of eavesdropping.
A MitM attack involves cybercriminals placing themselves between the user and the application when it occurs in the public domain and altering communication.
They can eavesdrop, and steal the data of others which will affect their privacy.
Also, they can hijack an account by faking the parties to get unauthorized access.
MitM attacks are capable of causing major losses for companies, which might result in uncontrollable data leakages.
They can be a source of valuable data, for instance, login credentials to return a site, people’s personal data, or financial information.
Denial-of-Service (DoS) and Distributed Denial-of-Service (DDoS)
Now, let’s take a look at Denial-of-Service (DoS) and Distributed Denial-of-Service (DDoS) Attacks, another critical category in the types of cyber security threats.
Their primary target is the overload of a network, a system, or a service with many requests beyond its capabilities of processing, thus making it slower to crash.
In the case of a DoS attack, the attacker overloads a Web server trying to slow down or stop it completely via a large number of request packets from a single source.
It presents itself as like a bully chronically annoying a business phone line making whoever the actual caller is unable to get through on the line.
Unlike a brute force attack which uses only one computer to penetrate a system, a DDoS or distributed denial-of-service makes use of multiple compromised computers that collectively try to disrupt the same system.
Such outages may cause interruptions of production, loss of revenue and containments of the brand reputation of the organization.
Through the utilisation of solid security measures and observing a close watch on your traffic network, you can defend the system from these types of cyber security threats.
SQL Injection
SQL injection is amongst the most dangerous types of cyber security threats.
Code injection approach is used by cybercriminals to perform SQL Injection attacks, and it is the main technique utilized while attacking data-driven applications.
The attacker uses malicious SQL codes as backend database manipulation tools to get information intentionally hidden before it can be viewed.
This information can be very confidential, such as making an impression of a business, contact lists, or personal information about customers.
SQLi (SQL injection ) is a security risk that comes as a result of its inherent simplicity and severity of effect.
An intruder might be able to bring about chaos in the database by writing only a few lines of code which is able to browse, modify, as well as delete data.
It’s like digital surveillance, which keeps you under the radar and is absolutely random.
Knowing SQL Injection and the ways it could lead to the loss of your digital assets is important in the digital world.
By approaching this issue with strong security measures in hand like input validation, parameterized queries, and stored procedures you can successfully stave off SQL Injection attacks.
Zero-Day Exploits
Next, we have Zero-Day Exploits, which is another important category related to the types of cyber security threats.
The Zero-day exploit denotes a software vulnerability unbeknownst to all of those involved in the threat mitigation process – beginning with the vendor of the target software.
The term “zero-day” was first coined due to the zero day span remaining for the developers to fix the vulnerability that had recently come to light, and possibly already utilized by hackers for malicious purposes.
Thus the digital realm does have trap-covers for their eventual utilisation.
These are exploitable points in software that hackers can possibly use to access a system for unauthorized purposes or to gain control over it.
These flaws can be of a special hazard since the software company doesn’t know the code is vulnerable and thus doesn’t come up with a fix.
The zero-day exploits may make things much worse.
A malicious activity like data theft, service disruption, or even system override could result.
These digital infiltrations are the secret spy missions, retracing steps behind your back.
Professional interest, zero-day exploits, and how they work, have a very important role in cybersecurity because you can identify possible weak points in your information systems and prevent cyberattacks or minimize their implementation.
By implementing your software with the version to be updated, dependable security agents, and information on the best approaches of security solutions, you can avoid zero-day exploits.
Conclusion
Finally, reaching the end of the article about the different types of cyber security threats, it is crucial to recall that knowledge is hands down the best weapon.
In the digital era, cyber-attacks might be an ongoing menace even now.
As a progressive step in the process of building immunity to these threats, it will be beneficial to understand the basic traits of the enemy, their techniques of action, and the harm they cause.
It is a proactive approach, information, and implementing the precautions that we need. It’s about not merely coping with and actually loving the digital world.
Throughout the digital world, bid us farewell with the confidence we have gained about different types of cyber security threats and the adventure we will need to utilize in the future for our safety.
There are many types of cyber security threats that are quite dangerous!
However, the strategy of shelters is much more defined and executable as well.
You May Like Also:
6 thoughts on “What Are The Different Types of Cyber Security Threats”